CIA

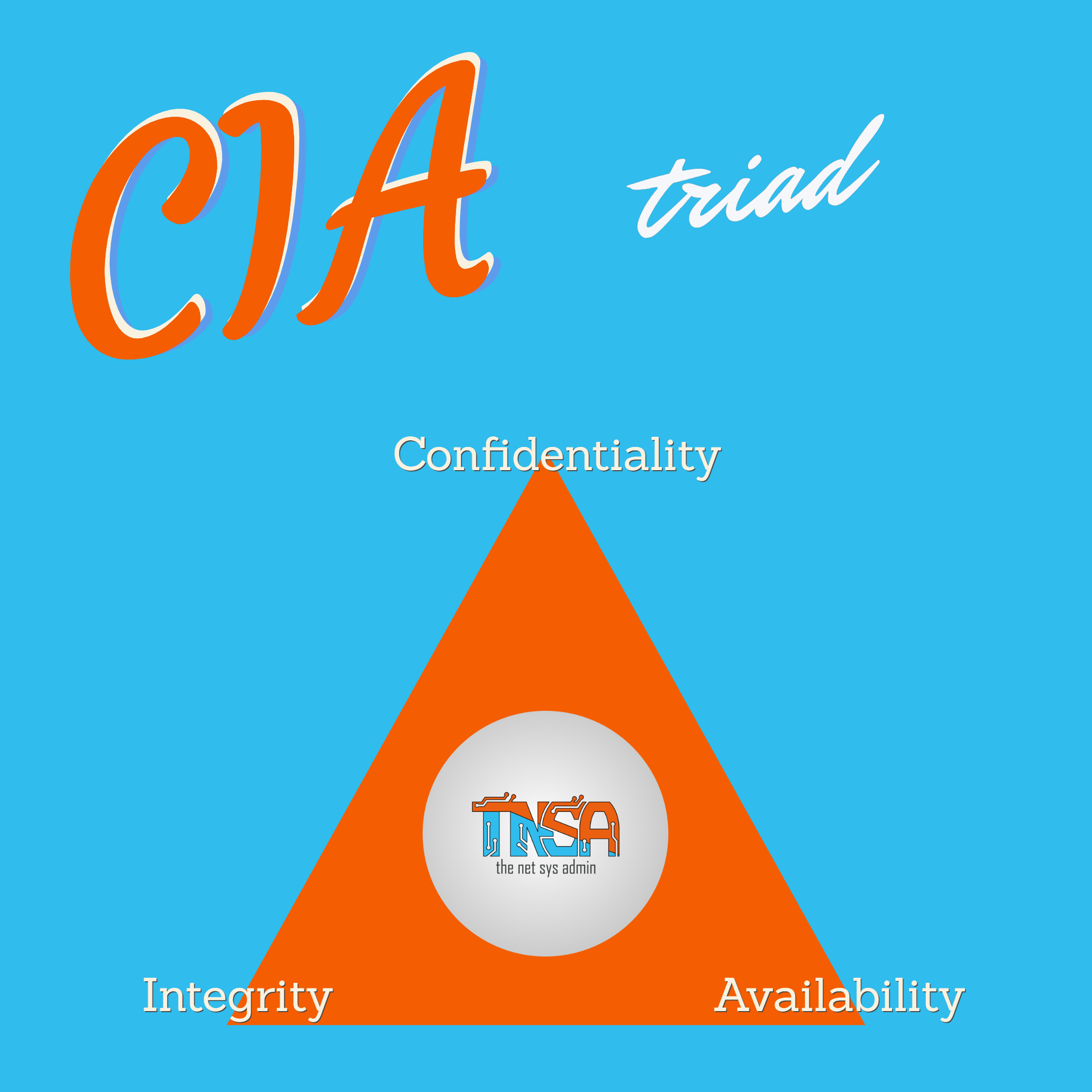
Today’s Objective is known as the CIA triad or AIC triad. Depends on what you read. Either way they mean the same thing. The C is for confidentiality, I for Integrity, and A for availability.
This objective falls under Domain 1 of the CBK – Security and Risk Management. The CIA triad is considered the foundational goal of any security infrastructure or program. All the security measures, tools, and training will have roots in the principals of CIA. While each principal is unique and accomplished a different goal they all work together intimately.
We’ll start with Confidentiality. When I think of something as confidential I think secret. For this concept the secrecy of data and resources is what you are concerned with. Whether it is while being stored (known as data-at-rest) or during in transmission (data-in-transit). Confidentiality can be accomplished by encrypting data, utilizing access controls, classifying data by criticality, and security awareness of personal. Some methods an attacker can use to obtain breach confidentiality are: (this is not an exhaustive list)
- Social Engineering
- Port scanning
- Shoulder surfing
- Escalation of privileges
- Eavesdropping
- Sniffing
- Capturing network traffic
Now moving on to Integrity. When most people think of integrity they are thinking about honesty. Integrity in security is not much different. When the organizations data, information, and systems maintain integrity they can be considered whole, complete, unaltered, and free of any corruption. Viruses are a perfect example of a method to compromise the integrity of a system since a virus can make unauthorized changes. While confidentiality is focused on secrecy, integrity’s focus is to ensure no unauthorized alterations happen to data while being stored or transmitted. To help me put this concept in action I like to imagine a scenario where a program that teachers use to track grades has a database that is hacked by a student. The student then modifies their grades. Because the grade change is an unauthorized change the data can no longer be trusted and therefore has lost integrity. A key aspect of integrity is non-repudiation. You will hear this term many times in your CISSP studies, and we will go into detail at another time. For now just know non-repudiation basically means that no one can deny having taken an action or sending a message (in the case of email)
Now for the A Availability. This should be perhaps the most familiar concept for network and systems admins. Availability is ensuring that your data and systems are accessible and can be accessed securely. General means to achieve availability is to provide redundancy and backups for your systems and data.